Canada & BGP Hijacking For over a decade (2010, 2018, 2019, 2020), China has quietly shown a pattern of hijacking global data flows by redirecting them through servers located in China, sometimes for minutes, other times for much longer, where the data could be copied onto Chinese Communist Party (CCP) networks and decrypted at leisure. One of the Read More…
Cyber Security and Emerging Threats
The NAOC’s Cyber Security and Emerging Threats Program features an in-depth analysis of latest trends, developments, and threats in international security. New security concerns are always on the horizon and our program seeks to examine these domains including global warming, natural resources, drones, urban conflicts, and cyberspace.
The program’s mandate is to keep Canadians informed on these rapidly developing and increasingly pivotal realms that are integral to all aspects of security.
The Geopolitics of Network Hegemony
The digital front of modern warfare and Great Power conflict increasingly occupies the minds of American and Chinese leaders. In this article, Touraj Riazi looks at the infrastructure that undergirds the digital world and how vital it is to the Chinese and American quest for “Network Hegemony.”
Zero Trust Networks: A New Normal for Cybersecurity?
What is Zero Trust in cybersecurity, and what are the reasons for the Biden administration’s push towards a Zero Trust architecture? In this article, Bryan Roh explains some of the reasons why the Zero Trust security model is gaining momentum in both the public and private sectors.
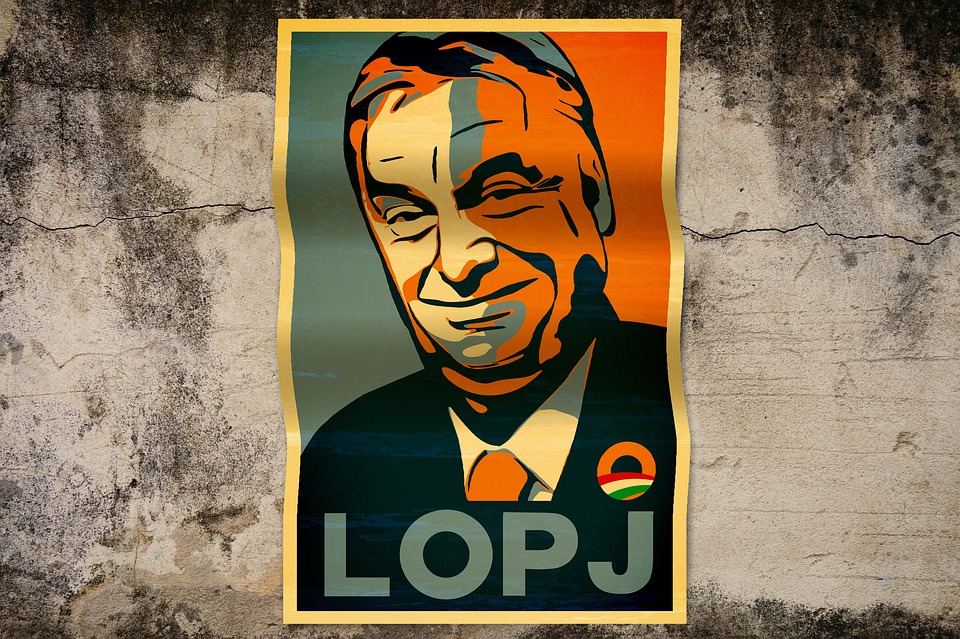
Democratic Backsliding in Former Communist Countries: Hungary
Signs of democratic backsliding in former communist countries in Europe have raised concern within the continent and beyond. In this second article of a three-part series on democratic backsliding, Tea Vasha explores how the justice system reform and other policy implementations in Hungary have contributed to undemocratic shifts.
Democratic Backsliding in Former Communist Countries: Poland
Does democratic backsliding constitute a threat to the peace and security of Europe and beyond? In the first article of a three-part series, Tea Vasha analyzes the reforms implemented in Poland during the Law and Justice Party’s rule and how they have contributed to a shift away from democratic norms.
Challenges to Cyber Resiliency Series – Diversity in Cyber Security
Are you interested in hearing about women and diversity in cyber security? Join us for the second panel of our Challenges to Cyber Resiliency Series to hear our panel of experts discuss the challenges facing diversity in cyber security and the importance of incorporating people from different backgrounds and experiences into the cyber field. Register here to Read More…
Should cyberattacks be considered an act of war?
From the advent of the U.S.’s development and releasing of the Stuxnet virus in 2010 to the more recent attacks on critical infrastructure, such as the Colonial Pipeline, cyberattacks have become an increasingly prominent and newsworthy facet of contemporary society and international relations. While by no means novel phenomena, amidst these growing developments and in Read More…
Colombia Protests, NATO Partnership, and Democratic Principles
Over the last two decades, NATO has advanced its enlargement policy, welcoming new members and partners. Colombia was the first – and currently, the only – Latin American country to become a NATO global partner, cooperating on issues such as cybersecurity and corruption. Both sides of this partnership work together to further their goals. Personnel Read More…
Lukashenko’s Gambit: Embattled Belarusian President Risks National Sovereignty Amidst Increasing Isolation from the West
In this article Griffin Cornwall examines the impact of the Belarusian Government’s dramatic arrests of Roman Protasevich and Sofia Sapega, the increased sanctions pressure from the West this action has brought, and the potential risks to Belarus’ national sovereignty brought by President Lukashenko’s retrenchment of his relationship to his longstanding ally, Russian President Vladimir Putin
The Need for Secure AI Design Frameworks and AI Model Security
AI technologies are becoming widely adopted in industries across the globe for their potential to revolutionize how organizations engage in business. For example, a report published in late 2020 by McKinsey suggests that organizations are increasingly viewing AI as a tool to generate value, and that the COVID-19 pandemic has further spurred business leaders to Read More…